.jpg)
Prioritising security in 2024: Why 2FA is vital for breach prevention


Want to keep your financial data safe? Then, two-factor authentication (2FA) should be non-negotiable. If you don’t currently use 2FA to access your financial systems, you could be putting your financial data at risk. This guide shows you why and how to implement 2FA.
- What is 2FA?
- How does 2FA work for breach prevention in the finance sector?
- Four types of 2FA
- Why is 2FA important for financial institutions?
- Best practices for implementing 2FA
- Two-factor authentication security measures from Payhawk:
- 2FA for breach prevention in finance: What to take away
By submitting this form, you agree to receive emails about our products and services per our Privacy Policy.
Have you ever used the password “123456”? No? How about “password”? No? Good to hear (and expected as a finance professional). But unfortunately, this might not be true for a few of your colleagues.
According to research from SafetyDetectives (looking at 9,056,593 passwords), the most commonly globally-used passwords are:
- 123456
- password
- 123456789
Yep, you read this right.
Cybersecurity risks are increasing. As more and more businesses are going digital, companies have better access to real-time spend info, and easier ways to move money, and more. So far, so good. But companies (and the industry) must also make sure that their — and their customers' — finances are safe by employing every cybersecurity tool in the box.
From June 2022 to June 2023, 640 cybersecurity threats were reported by UK financial services firms to the Information Commissioner's Office (ICO), an increase of 240% from the previous year. With threats to data rising so rapidly and constantly, fintechs and software companies can't afford to let their guard down.
Two-factor authentication is an effective way to protect customer data by adding an extra layer of security instead of relying on just a password. This extra layer of protection makes it more difficult for threat actors to access sensitive information.
In this guide, we explore the importance of 2FA authentication, how it works, the different types, and best practices for implementation.
Secure spending made easy: Read about our robust safety features
What is 2FA?
2FA is a login process requiring two different authentication types before letting the user into the system. These two forms of identity verification are usually a password or a PIN, followed by a code from an authentication app or text message.
Introducing these two steps makes it much easier for financial institutions to keep their data safe and secure and prevent data breaches. The main benefit of this approach is that if the password is compromised, the threat actor still won’t be able to access the system without getting the second form of authentication from the authenticator app.
What about 2FA in the wild? It’s big. Companies are adopting multi-factor authentication much more frequently to protect sensitive information. In fact, the use of MFA has increased by 51% from 2017 to 2021, and it's projected to have a $20 billion market share by 2025.
Conclusion: If you don’t require 2FA to access your financial data, you should implement it now.
How does 2FA work for breach prevention in the finance sector?
By implementing 2FA, you will significantly improve your system security. According to Microsoft, multi-factor authentication can block more than 99.9% of account compromise attacks.
Here’s how 2FA helps prepare the finance sector for breach prevention:
- Protecting financial controllers from password theft: SpyCloud found that of those who experienced data breaches in 2021, an overwhelming 70% still used the same passwords. The same research also found that 64% of Fortune 1000 employees reused passwords over multiple sites. Passwords can still be breached or lost, so adding a level of security in 2FA ensures that you can avoid any major consequences, even if it does happen to your company.
- Attackers using phishing techniques can't gain access easily: Suppose a user has been tricked into revealing their passwords through a phishing attack, e.g., clicking links in spam emails. In that case, 2FA will stop the threat actor from using that password. The second-factor authentication will kick in before they can gain access (giving you time to flag the log-in attempt as malicious and block the threat actor).
- Protects against password guessing: Online systems are vulnerable to brute force attacks trying common passwords. But with 2FA in your arsenal, these attacks can't succeed – unless the threat actor has also stolen your users' 2FA credentials, which is far more difficult and less likely.
Key Takeaway: 2FA technology significantly decreases both the possibility of unauthorized account access and helps safeguard info in case of a breach. For these reasons, you should implement 2FA for all users accessing your financial systems.
Four types of 2FA
Here are the most common types of 2FA:
SMS Codes
Although not foolproof, SMS codes are a quick and easy way to access one-time passcodes. A word of warning: Although generating SMS codes is better than just relying on a single password, there is a possibility that a threat actor can intercept these messages or perform an attack called SIM Swapping.
Time-based one-time password (TOTP)
Apps like Google Authenticator or Microsoft Authenticator are free for users to download and immediately provide a secure way to generate time-based one-time passwords or TOTPs. After typing in their password, the user usually scans a QR code on the site they’re trying to access, generating a one-time access code. These apps are a more secure way to implement 2FA than SMS codes.
FIDO security keys
A FIDO security key is a physical device that protects your authentication and acts as an additional physical security layer besides your password. Although relatively inexpensive, you must pay for these keys; the more users you need to purchase, the more costs will stack up. Although they’re an excellent security measure if a user loses the key, locking them out of the associated account will still create an unnecessary hassle (and losing these small things is quite easy)
Biometrics
Apart from making you feel like you’re in a sci-fi movie, biometrics technology has some fantastic security benefits. The rise of biometrics in software development is exciting and provides users with a unique way of quickly accessing systems. Biometrics uses fingerprint scanning and facial recognition technologies to provide a more personal layer of security for each user account. Check with your finance software provider; not all solutions support this technology.
Why is 2FA important for financial institutions?
All financial institutions should prioritize strong authentication, protecting corporate funds and customer data.
- Financial institutions are high-risk targets: Financial institutions are prime targets for threat actors and scammers, particularly since the rise of digital banking technology. This industry is one of the most at risk for data breaches and other cybercrimes.
- Data breaches won’t be limited to financial data: Many financial firms store a lot of personal information, from addresses to names and other sensitive personal data. That’s alongside business data like account numbers and transaction details, which would be available to threat actors in case of a breach.
- Fast authentication process with 2FA: Users accessing this software need a fast and reliable multi-factor authentication process that doesn’t delay transactions or business operations. 2FA is relatively fast and simple once set up, and without robust security features like 2FA, user accounts can become compromised.
Implementing reliable and robust 2FA on financial systems should be a non-negotiable security practice. Without it, you’re leaving user data vulnerable and opening them up to potentially costly security incidents.
Best practices for implementing 2FA
Implementation matters. When it comes to security implementation practices, there are the good, the bad, and the ugly.
Here are some best practices to keep in mind:
- Make enrolment mandatory for all users. You don't want to leave it down to individual users to implement multi-factor authentication. Ensure it's mandatory for all users so you can properly secure your financial data
- Educating users is key. Take time to explain 2FA, how it works, and why it's important. Be sure to show them how to use an authenticator app if you're using one to avoid confusion and low adoption
- Streamline the user experience. Make using 2FA effortless for everyone. Find a solution that minimizes the steps required to confirm identity. Make it as simple as possible
- Support multiple factors. Don't just force one type of 2FA onto your users; offer numerous choices, from SMS codes to biometrics
- Choose software carefully. Make implementation even easier with secure, forward-thinking financial software that already uses 2FA. Like expense management software from us at Payhawk

Two-factor authentication security measures from Payhawk:
At Payhawk, we take security seriously.
We’re committed to delivering an accessible financial system for business expense management while ensuring your sensitive data and information are as secure and protected as possible against cyber threats.
Any access to platform servers and management systems requires the user to undergo 2FA (including biometric authentication for accessing our Payhawk mobile app).
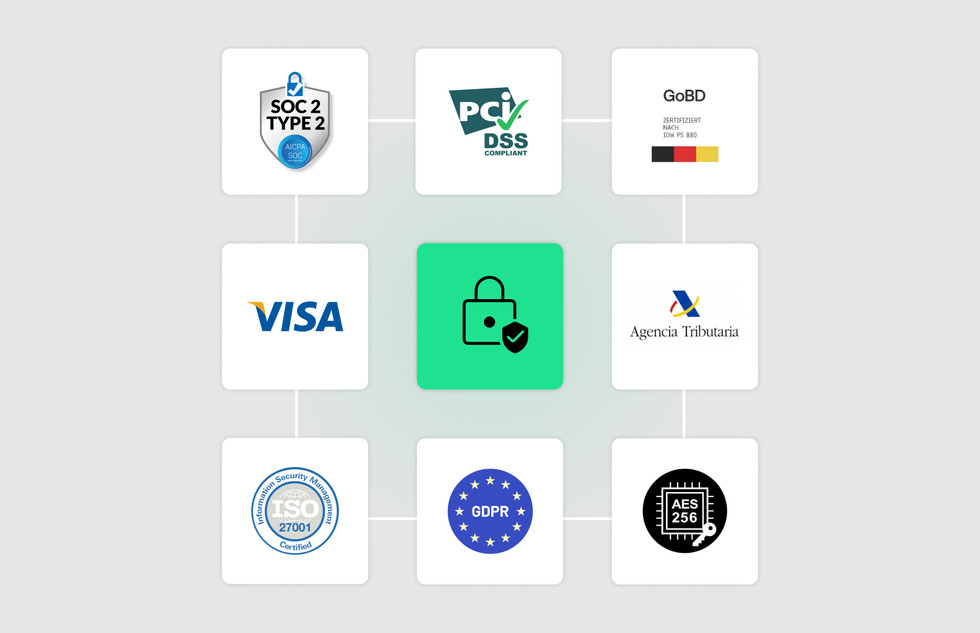
Moreover, we have all the required security certifications and ‘Threat-proof’ encryption technology governing all transactions.
What other security measures do we implement?
- Encrypted data using industry-standard AES 256.
- Single sign-on with Okta, Microsoft Azure, and Google Workspace.
- 3D security payments layer to protect your online transactions.
- ISO 27001, SOC 2 Type 2 and PCI DSS-compliant
Additionally, we carry out sporadic stress tests to check if the owner of the user ID still works for your company in the same capacity.
Read more about our security certifications here.
2FA for breach prevention in finance: What to take away
Yes, cybercriminals pose an increasing threat. However, protecting your data with 2FA can significantly reduce these threats and is especially easy to implement, providing you pick the right software solutions.
By increasing the complexity of your system sign-in requirements, you can say goodbye to reusable credentials and imminent cyber-attacks and instead embrace quick and simple multi-factor authentication for effortless data protection.
Schedule a demo to learn more about our secure time-saving solution.
Trish Toovey works across the UK and US markets to craft content at Payhawk. Covering anything from ad copy to video scripting, Trish leans on a super varied background in copy and content creation for the finance, fashion, and travel industries.
Related Articles
.jpg)

The top four HRIS features for data security & fraud prevention

